Cloud Migration: Benefits, Challenges, and Best Practices (2026 Guide)
A practical, decision-ready guide to cloud value, risks, and a proven path to migrate with confidence.
Cloud migration—moving applications, data, and infrastructure from on-premises environments to cloud platforms—has shifted from “nice to have” to a core IT strategy for many organizations. The promise is compelling: elastic scale, faster delivery, global reach, and modern security tooling. But migrations can also create new operational complexity, cost surprises, and governance gaps if they’re rushed or under-planned.
This guide breaks down the benefits and challenges of moving to the cloud, then gives a practical playbook you can apply—whether you’re migrating one workload or an entire portfolio.
What “Cloud Migration” Actually Means
Cloud migration isn’t one decision—it’s a set of choices:
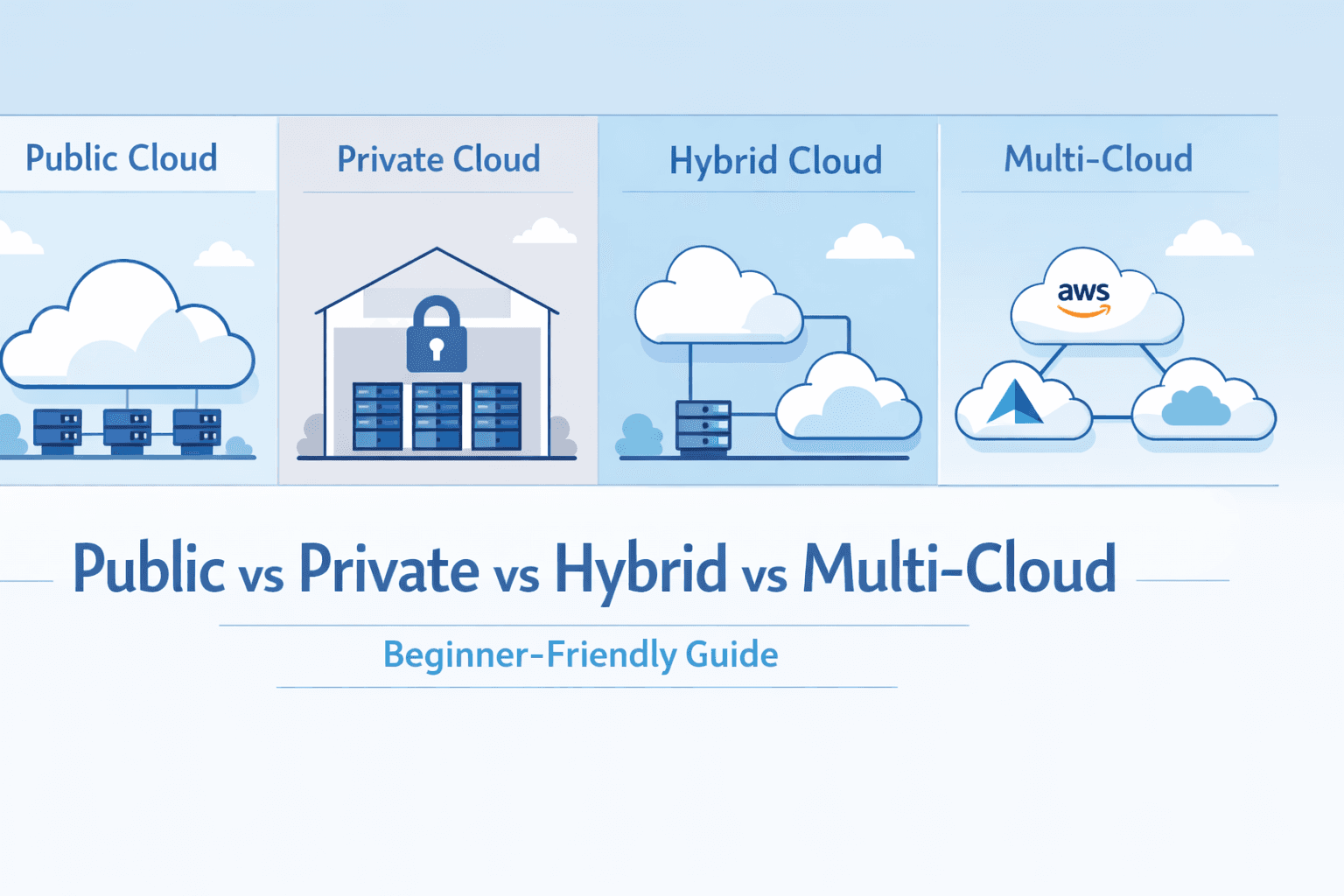
Deployment model: Public cloud, private cloud, or hybrid/multi-cloud
Service model: IaaS (infrastructure), PaaS (platform), SaaS (software)
Migration approach: Lift-and-shift, re-platform, refactor, replace, retire, retain
Reader quick-check (30 seconds)
Pick the option that best matches your situation:
We need speed → likely lift-and-shift or re-platform
We need modernization → likely refactor (or replace with SaaS)
We need compliance control → likely hybrid with strong governance
We need cost predictability → likely FinOps-first approach, then migrate
Benefits of Moving to the Cloud
1) Elastic scalability (without overbuying)
On-prem environments often require buying for peak demand. Cloud platforms make it easier to scale up for spikes and scale down when demand drops. That’s not just convenience—it can change your business model (seasonal campaigns, global launches, bursty analytics).
Interactive prompt:
If you doubled traffic tomorrow, would your current stack degrade, fail, or scale?
2) Faster delivery and better developer velocity
Cloud-native tooling (managed databases, CI/CD integrations, serverless services, containers) reduces undifferentiated heavy lifting. Teams can ship features faster when provisioning is measured in minutes, not weeks.
Signal to track: deployment frequency, lead time for changes, and mean time to restore (MTTR).
3) Reliability and resilience improvements
Major cloud providers offer highly available building blocks across zones and regions. When used correctly, you can build better disaster recovery (DR) and business continuity than many organizations can afford on-prem.
Reality check: cloud resilience is not automatic. It’s an architectural choice.
4) Security capabilities that are hard to replicate on-prem
Cloud ecosystems provide mature security tooling: centralized identity, encryption at rest and in transit, key management, logging/monitoring, posture management, DDoS protection, and automated policy enforcement.
Key point: Cloud security is a shared responsibility. You inherit strong primitives, but you must configure and operate them correctly.
5) Cost agility and improved cash flow
Cloud shifts large upfront capital spending (CapEx) toward operating expenses (OpEx). This can improve cash flow and align spend to actual usage—especially when you design for elasticity and right-size continuously.
FinOps lens: cost savings come from governance + optimization, not from “moving” alone.
6) Global reach and performance options
Need low latency for users in multiple geographies? Cloud regions, CDNs, edge services, and managed load balancing can improve performance and reduce operational burden.
7) Access to modern capabilities (AI/ML, analytics, event streaming)
Cloud platforms make advanced services accessible—data lakes, managed warehouses, real-time streaming, AI model hosting, and automation. For many organizations, this is the modernization payoff.
Challenges of Moving to the Cloud (and How to Handle Them)
1) Cost overruns and “bill shock”
Common causes:
Overprovisioned instances and unused resources
Data egress charges and cross-region traffic
Always-on environments and non-optimized storage
Lack of tagging and ownership
Mitigation checklist
Establish cost allocation tags (owner, app, env, cost center)
Set budgets + alerts (per team/app/environment)
Enforce auto-shutdown for non-production
Implement rightsizing and reserved capacity where appropriate
Track unit economics (e.g., cost per transaction)
2) Security and compliance misconfiguration
Cloud increases the speed of change—so misconfigurations can propagate quickly.
Common risks
Over-permissive IAM roles (“admin everywhere”)
Publicly exposed storage or services
Weak secrets management
Insufficient logging, monitoring, and incident readiness
Mitigation
Use least privilege IAM + short-lived credentials
Centralize secrets (vault/managed secrets service)
Turn on audit logging and keep it immutable
Baseline with policies (“guardrails”) and automated checks
3) Migration downtime and data integrity issues
Data movement is often harder than compute movement: dependencies, replication, cutover timing, and rollback planning.
Mitigation
Classify data: RPO/RTO targets, data sensitivity, residency requirements
Use staged migration: replicate → validate → cutover
Rehearse cutover like a release (with runbooks and rollback)
4) Application compatibility and technical debt
Some apps were never designed for elastic scale, ephemeral infrastructure, or distributed networking. Lift-and-shift may “work,” but it can also move problems to a more expensive environment.
Mitigation
Assess each workload for the right “R” strategy: rehost, re-platform, refactor, replace, retire, retain
Prioritize modernization for high-change, high-value systems
Avoid refactoring everything at once—target bottlenecks first
5) Vendor lock-in concerns
Using managed services can accelerate delivery, but it can also reduce portability.
Mitigation
Define a portability stance by workload (not one-size-fits-all)
Use containers and open standards where it matters most
Keep data access patterns and schemas documented and exportable
Negotiate contracts and exit plans early
6) Skills gap and operating model change
Cloud migration is a people/process change as much as a technical shift. Teams must learn cloud architecture, automation, security, and FinOps practices.
Mitigation
Upskill: training + pairing + internal enablement
Establish a Cloud Center of Excellence (CCoE) or enablement team
Shift left: security, reliability, and cost into delivery workflows
7) Governance complexity (multi-account, multi-team, multi-everything)
Cloud enables rapid creation of resources. Without governance, sprawl appears fast.
Mitigation
Define landing zones: accounts/subscriptions, network, identity, logging
Standardize templates (infrastructure-as-code)
Use policy-as-code for guardrails and approvals
Best Practices: A Practical Cloud Migration Playbook
Step 1: Build a clear business case
Tie migration to measurable outcomes:
faster release cycles
better uptime
reduced time-to-provision
improved security posture
faster analytics/AI capability delivery
Interactive prompt:
Which KPI matters most to leadership: speed, reliability, cost, or security?
Step 2: Inventory and classify workloads
Create a lightweight application portfolio view:
criticality (tier 0/1/2/3)
dependencies (data stores, APIs, network)
compliance needs
performance and latency constraints
current pain points and technical debt
Then pick the right migration strategy per workload (the “6 Rs”).
Step 3: Establish the foundation (landing zone)
Before migrating apps, set up:
identity and access (SSO, IAM roles, MFA)
network segmentation and connectivity (VPN/Direct Connect/ExpressRoute)
centralized logging/monitoring
baseline security controls and encryption
resource tagging, budgets, and cost reporting
This reduces rework and prevents “shadow cloud.”
Step 4: Choose the right migration path for each workload
Use a simple decision matrix:
Rehost (lift-and-shift): fastest, least change, may not optimize cost
Re-platform: moderate change, better operations, still relatively fast
Refactor: best long-term benefits, highest effort/risk
Replace (SaaS): fastest to modernize, changes process and ownership
Retire: remove what you don’t need
Retain: keep on-prem for technical/regulatory reasons
Step 5: Migrate in waves (pilot → scale)
Start with:
low-risk, high-learning workloads
clear success criteria
a repeatable pipeline (IaC + CI/CD + security checks)
Then scale to more critical systems once the playbook is stable.
Recommended wave model
Pilot (2–6 apps) → validate standards and tooling
Wave 1 (customer-facing or internal high-impact)
Wave 2 (core systems + data platforms)
Optimization phase (FinOps + reliability hardening)
Step 6: Design for reliability, not just “it runs”
Cloud architectures should address:
multi-zone redundancy for critical workloads
backups with regular restore tests
DR plan (cross-region where needed)
SLOs/SLAs and error budgets
observability (logs, metrics, traces)
Step 7: Implement FinOps from day one
FinOps is the practice of managing cloud spend with shared accountability across engineering, finance, and product.
Minimum viable FinOps
tagging standards + ownership
budget alerts
monthly cost reviews per product/team
automated cleanup (idle resources)
rightsizing + reserved capacity strategy
Step 8: Secure-by-default through automation
Make secure choices the path of least resistance:
infrastructure-as-code with approved modules
policy checks in CI/CD (misconfig detection)
secrets management integrated into pipelines
continuous posture monitoring and patching
Practical Checklists (Copy/Paste)
Cloud readiness checklist
Workload inventory completed and categorized
Dependencies mapped (data, network, identity, integrations)
Security baseline defined (IAM, encryption, logging)
Landing zone ready (accounts, network, monitoring)
Migration approach per workload chosen (6 Rs)
Cutover and rollback plans documented
DR and backup strategy validated
Cost controls in place (tags, budgets, alerts)
Ops model defined (incident response, on-call, SLOs)
Training/enablement plan running
Pre-cutover checklist
Data replication validated (checksums/consistency tests)
Performance tests completed
Monitoring dashboards and alerts live
Access reviews completed (least privilege)
Runbooks and escalation paths confirmed
Rollback tested (or at least rehearsed)
Stakeholders notified and downtime window approved
Common Myths (Quick Debunk)
“Cloud is always cheaper.” Not automatically. Cost efficiency requires governance and design.
“Cloud is secure by default.” Cloud gives strong primitives; security depends on configuration and operations.
“Lift-and-shift is a final state.” Usually it’s a stepping stone—optimization often follows.
Conclusion: The Best Cloud Migration Is Intentional
Cloud migration can unlock speed, reliability, and modern capabilities—but only when paired with the right foundation, governance, and operating model. The most successful organizations treat migration as a portfolio program: they prioritize high-value workloads, build repeatable patterns, and continuously optimize cost and security.